Course Curriculum
| Introduction | |||
| The goals of Network defense | 00:05:00 | ||
| The overview of the different types of network defense approaches | 00:05:00 | ||
| The different types of Network security controls | 00:08:00 | ||
| Basic Linux concepts | 00:03:00 | ||
| Identification, authentication and authorization | |||
| The different types of identifications (overview) | 00:02:00 | ||
| The different types of authentications (overview) | 00:05:00 | ||
| The different types of authorization (overview) | 00:03:00 | ||
| Network security controls: physical controls | |||
| Understanding the importance of physical security | 00:04:00 | ||
| The different physical security attack vectors | 00:04:00 | ||
| Understanding the various environmental controls | 00:04:00 | ||
| Network security controls: technical controls | |||
| Understanding Network segmentation and its types | 00:05:00 | ||
| Understanding the different types of firewalls and their roles | 00:06:00 | ||
| Understanding the different types of IDS/IPS and their roles | 00:05:00 | ||
| The different types of proxy servers and their benefits | 00:04:00 | ||
| Fundementals of VPN and their importance in a network: Part 1 | 00:05:00 | ||
| Fundementals of VPN and their importance in a network: Part 2 | 00:05:00 | ||
| Overview of antivirus/anti-malware software | 00:05:00 | ||
| Virtualization and cloud computing | |||
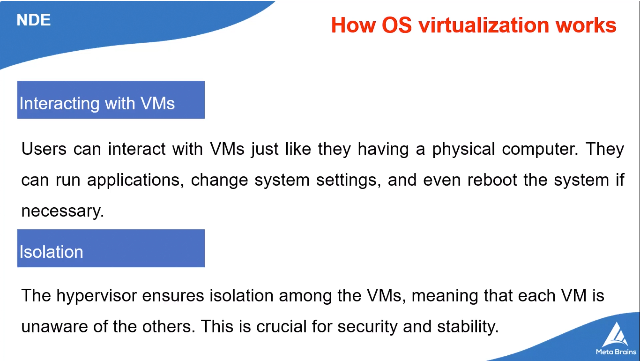
| Understanding virtualization and its components | 00:06:00 | ||
| OS virtualization security | 00:06:00 | ||
| Cloud computing and its benefits | 00:04:00 | ||
| Overview of different types of cloud computing service | 00:05:00 | ||
| Importance of cloud computing and its best practice | 00:05:00 | ||
| Wireless network security | |||
| Wireless network encryption mechanism | 00:05:00 | ||
| Understanding the different types of wireless network authentication methods | 00:10:00 | ||
| Wireless security measures and wireless security tools | 00:05:00 | ||
| IoT device Security | |||
| Understanding IoT architecture and communication models | 00:10:00 | ||
| Understanding the best practice tool for IoT for security | 00:06:00 | ||
| Cryptography and public key infrastructure | |||
| Cryptography techniques | 00:06:00 | ||
| The different Encryption algorithm | 00:06:00 | ||
| The different hashing algorithm | 00:05:00 | ||
| Different cryptography tools and hash calculators | 00:03:00 | ||
| PKI infrastructure | 00:04:00 | ||
| Data security | |||
| The different data security controls for data encryption | 00:24:00 | ||
| File encryption, removable-media encryption and disk encryption | 00:05:00 | ||
| Methods and tools for data backup retention: Part 1 | 00:04:00 | ||
| Methods and tools for data backup retention: Part 2 | 00:06:00 | ||
| DLP&S (data loss prevention and solutions) | 00:04:00 | ||
| Mini Projects | |||
| The implementation of an IDS/IPS (Snort) on a Linux based system | 00:04:00 | ||
| Installation of snort and its libraries. (Both Linux and ubuntu) | 00:04:00 | ||
| Configuration of snort for IDS/ IPS functionalities | 00:04:00 | ||
| Time-zone configuration and swap files in firewall | 00:03:00 | ||
| How to set-up a VPN | 00:02:00 | ||
| Firewall configuration | 00:06:00 | ||
Instructors
18 STUDENTS ENROLLED
 Food Hygiene
Food Hygiene Health & Safety
Health & Safety Safeguarding
Safeguarding First Aid
First Aid Business Skills
Business Skills Personal Development
Personal Development