Course Curriculum
| Topic 1: Introduction and Basics | |||
| 0- Ethical Hacking And And Network Security – Course Promo | 00:05:00 | ||
| 1- Importance Of Ethical Hacking | 00:02:00 | ||
| 2- Basic Cybersecurity Terminology | 00:05:00 | ||
| 3- Critical Software Essentials | 00:02:00 | ||
| Topic 2: Setting Up Your Environment | |||
| 4-Installing Virtual Box On Windows 10 | 00:04:00 | ||
| 5- Installing Kali Linux In A Virtual Environment | 00:05:00 | ||
| 6- Starting And Configuring Kali Linux | 00:01:00 | ||
| 7-Understanding Kali Linx Terminal | 00:05:00 | ||
| Topic 3: Anonymity and Privacy Tools | |||
| 8- Installing Tor On Kali Linux | 00:05:00 | ||
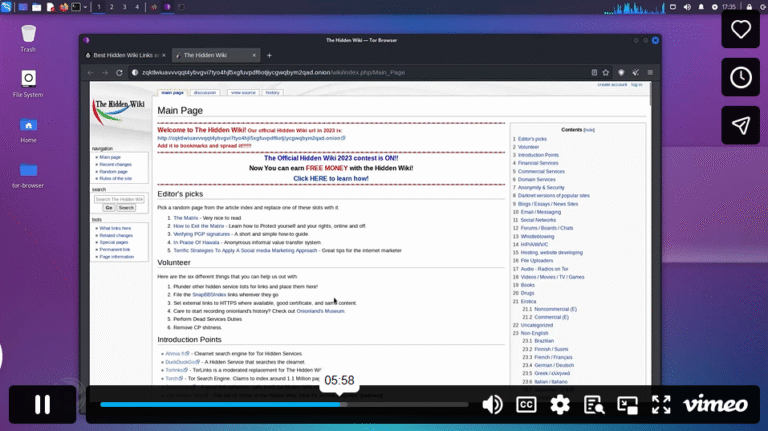
| 9-Vaccessing The Hidden Wiki And Dark Web Using Tor | 00:09:00 | ||
| 10- Installing And Using Anonsurf | 00:09:00 | ||
| 11- Install And Use Vpn In Kali Linux | 00:07:00 | ||
| 12- Using Proxychains in Kali Linux | 00:08:00 | ||
| Topic 4: Network Configuration and Monitoring | |||
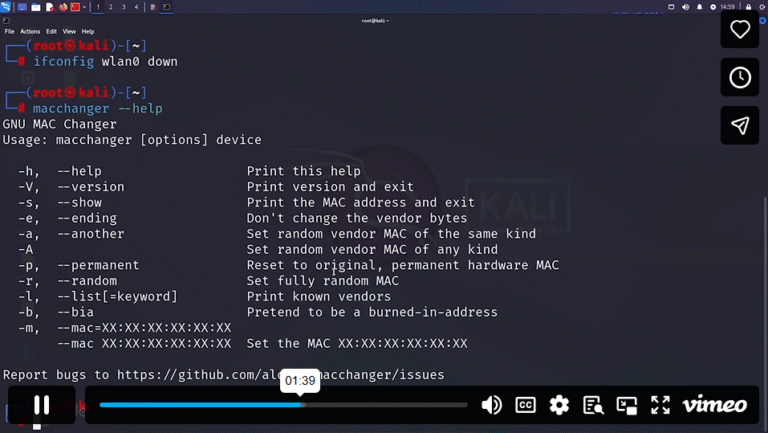
| 13- Changing The Mac Address (Part I) | 00:05:00 | ||
| 14- Changing The Mac Address (Part Ii) | 00:03:00 | ||
| 15- Connecting Wireless Network Adapters | 00:05:00 | ||
| 16- Enabling Monitor Mode In Your Network Adapter | 00:03:00 | ||
| 17- Enable Monitor Mode Manually | 00:03:00 | ||
| Topic 5: Scanning and Mapping Networks | |||
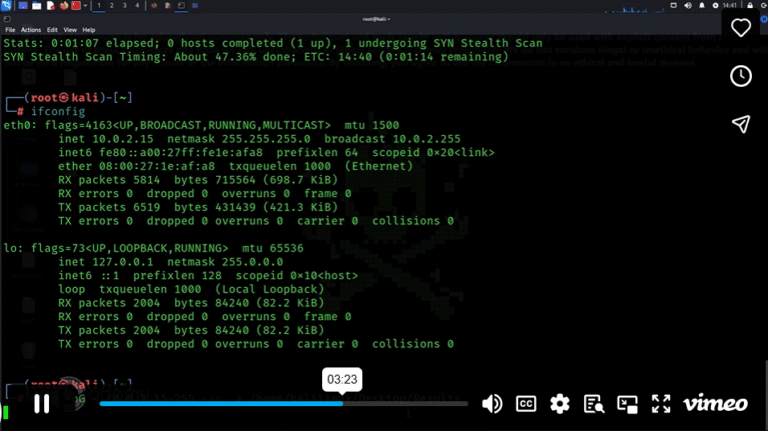
| 18- Working With Nmap | 00:06:00 | ||
| 19- Advanced Scanning With Nmap | 00:05:00 | ||
| Topic 6: Wi-Fi Hacking Techniques | |||
| 20- Overview Of Wifi Hacking | 00:04:00 | ||
| 21- Attacking Wifi Using Fern Wifi Cracker | 00:05:00 | ||
| 22- Exploring Word Lists Bop S C R K Technique | 00:05:00 | ||
| 23- Dealing With Rockyou Wordlists | 00:07:00 | ||
| 24- Wi-Fi Hacking Using Aircrack-Ng And Airodump-Ng | 00:06:00 | ||
| 25- Dos Attack On A Wireless Network | 00:07:00 | ||
| Topic 7: Advanced Anonymity and Concealment | |||
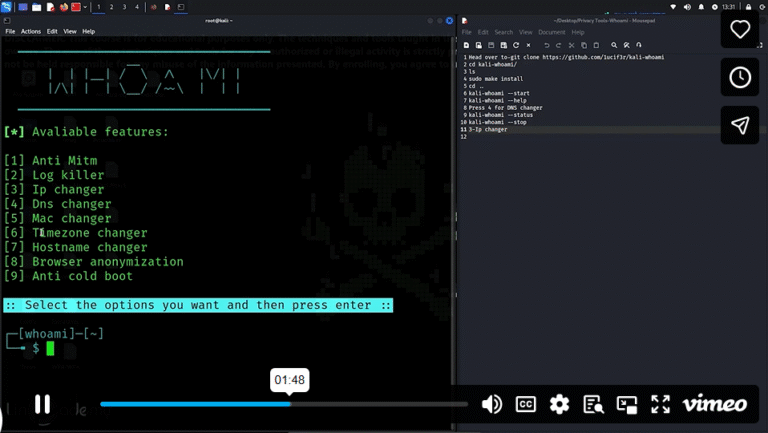
| 26- Identity Concealment Elevating Anonymity | 00:03:00 | ||
| 27- Utilizing Rootkit Detection Tools | 00:07:00 | ||
| Topic 8: Specialized Tools and Techniques | |||
| 28- Shodan – Exploring Iot Connectivity | 00:04:00 | ||
| 29- Keylogger Mastery Utilizing Beelogger For Keystroke Capture | 00:09:00 | ||
| 30- Employing Saint Spyware For Attacking Windows Os | 00:06:00 | ||
| Topic 9: Penetration Testing and Exploitation | |||
| 31- Penetration Testing Using Metasploit (Part I) | 00:07:00 | ||
| 32- Penetration Testing Using Metasploit (Part 2) | 00:08:00 | ||
| 33- Gaining Access To Android Devices With Androrat | 00:10:00 | ||
| 34- Windows Access Via Curl- A Remote Connection Approach | 00:04:00 | ||
| Topic 10: Encryption and Data Security | |||
| 35- Windows Encryption – Exploring Pgp | 00:11:00 | ||
| 36- Ultimate Encryption Guide- Secure Your Data With Kali Linux | 00:07:00 | ||
| Topic 11: Network Analysis and Freelance Success | |||
| 37- Master Wireshark Installation & Advanced Command Line Usage | 00:06:00 | ||
| 38- Unlocking Ethical Hacking Freelance Success | 00:05:00 | ||
Instructors
2 STUDENTS ENROLLED
 Food Hygiene
Food Hygiene Health & Safety
Health & Safety Safeguarding
Safeguarding First Aid
First Aid Business Skills
Business Skills Personal Development
Personal Development